0 results for 'Apache'

Lessons Learned From the Overuse of ESI Protocols
ESI protocols have become a Frankenstein monster of requirements that create obligations well beyond the Federal Rules of discovery, addressing a vast array of discovery topics including search terms, privilege logs and technology-assisted review. What lessons can we take away from the overuse of ESI protocols?
Supreme Court Will Consider Government's Duty to Fund Tribal Health Care
The dispute pits the federal government against tribes regarding the Indian Self-Determination and Education Assistance Act's funding provisions.
$240M Verdict: Law Firms Join Forces for Massive Victory
"Entrepreneurs should also take heart knowing that regardless of the size or scale of their company, patents will be enforced and protected by the courts," StreamScale attorney Jamie McDole said.
Ryan, LLC v. National Union Fire Ins. Co.
A Texas appellate court found the $346,612 paid to Weaver was an unlawful taking by Weaver to the deprivation of Ryan and, thus, there is coverage under the Employee Theft provision of the policy.
Why the GC for Virtru Became an Open-Source Crusader
"I really am a believer that technology should not control us; we should control technology. And without open source, I don't see how we could do that."View more book results for the query "Apache"

City of Unalaska v. Nat'l Union Fire Ins. Co.
"The litigation trends in the cyber insurance space confirm the need for policyholders to review the wording of their policies carefully with their risk managers, brokers, and advisers," say Cindy Jordano and Adam Ziffer of Cohen Ziffer Frenchman & McKenna.
After 25 Years, Houston Trial Boutique Hicks Thomas Preps for Another 25
Trial boutique Hicks Thomas, founded in 1997 by 10 litigators who left Andrews & Kurth is giving younger partners more responsibility to ensure the firm has staying power.
Data Security Company Hires Veteran Open-Source Lawyer as Legal Chief
Mishi Choudhary is taking the legal reins of Virtru, which helps more than 7,000 organizations safeguard and encrypt data.
Creative Approaches to IP in Web3
As the NFT space matures, it will be fascinating to see what new types of utility are bundled with IP rights and what types of bundling approaches work to spur increased innovation and increase the overall value of NFT projects.
Keep Vigilant and Carry On: How Law Firms Can Learn from Cybersecurity Cautionary Tales
Looking back at the past year of cybersecurity incidents and breaches, it is clear that hackers are getting smarter and more creative. Legal IT professionals can learn from these examples and strengthen their firm's security network and protocols accordingly.Trending Stories
- 1The Law Firm Disrupted: Playing the Talent Game to Win
- 2A&O Shearman Adopts 3-Level Lockstep Pay Model Amid Shift to All-Equity Partnership
- 3Preparing Your Law Firm for 2025: Smart Ways to Embrace AI & Other Technologies
- 4BD Settles Thousands of Bard Hernia Mesh Lawsuits
- 5A RICO Surge Is Underway: Here's How the Allstate Push Might Play Out
Featured Firms
Law Offices of Gary Martin Hays & Associates, P.C.
(470) 294-1674
Law Offices of Mark E. Salomone
(857) 444-6468
Smith & Hassler
(713) 739-1250
More from ALM
- Morgan & Morgan Class Action Attorneys Detail Pathway to Success Within Cybersecurity and Data Privacy Practice 1 minute read
- Holwell Shuster & Goldberg Partners Leverage 'Hostile' Witnesses to Secure $101 Million Verdict Against Walmart 1 minute read
- Legal Speak at General Counsel Conference Midwest 2024: Mike Andolina, Partner, White & Case 1 minute read
Resources
Strong & Hanni Solves Storage Woes--Learn How You Can, Too
Brought to you by Filevine
Download Now
Meeting the Requirements of California's SB 553: Workplace Violence Prevention
Brought to you by NAVEX Global
Download Now
The Benefits of Outsourcing Beneficial Ownership Information Filing
Brought to you by Wolters Kluwer
Download Now
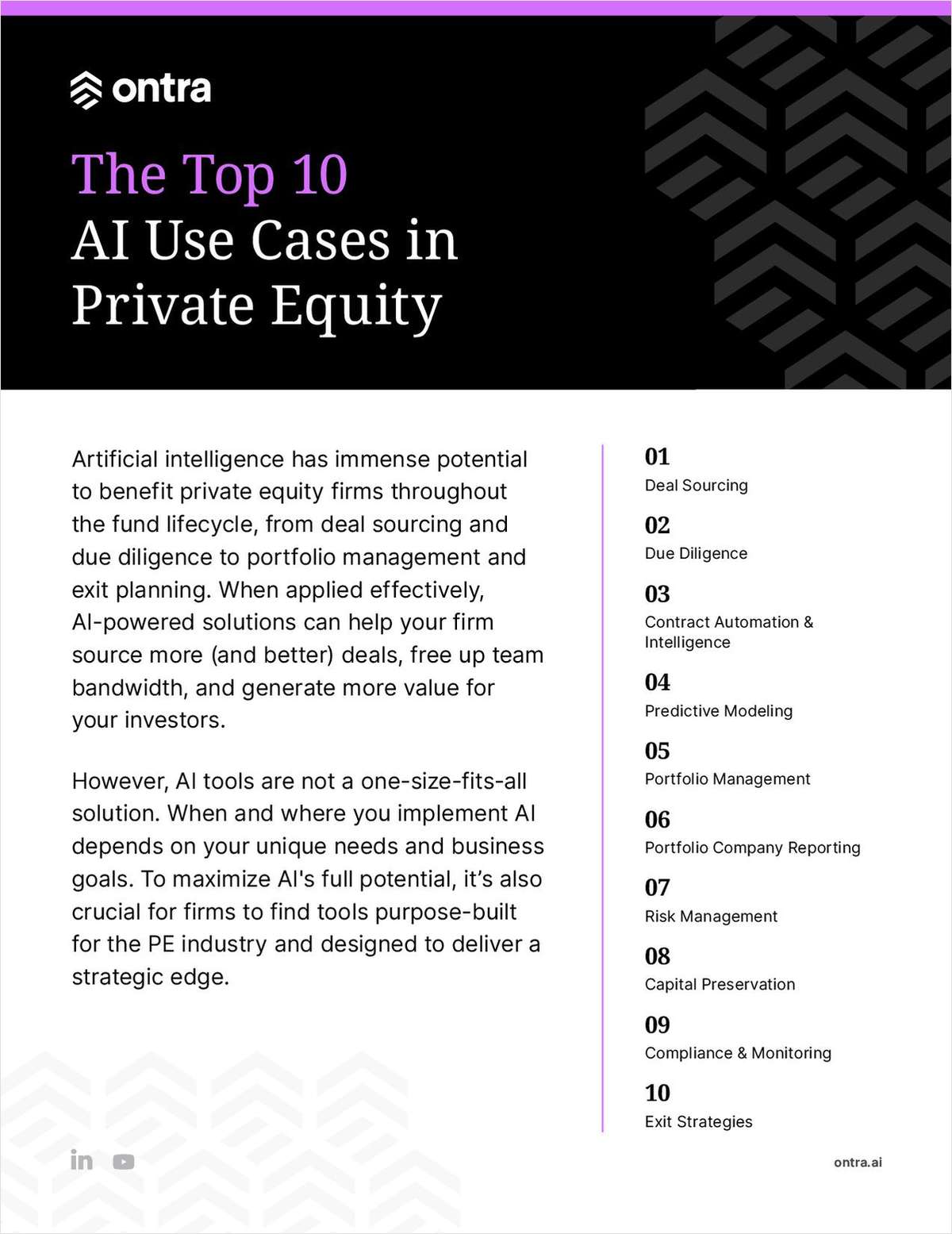
The Top 10 AI Use Cases in Private Equity
Brought to you by Ontra
Download Now



